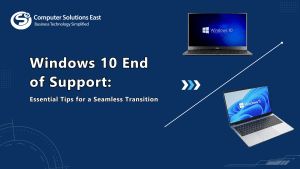
Why Upgrading to Windows 11 is a Game-Changer for Your Business
In today’s fast-paced digital landscape, businesses need an operating system that is secure, efficient, and built for modern workflows. Microsoft’s …
Continue reading “Why Upgrading to Windows 11 is a Game-Changer for Your Business”